This is Part 1 in my Configuring 802.1x Authentication for Windows Deployment series. Be sure to check out all of the other parts here.
The Anatomy of an 802.1x Configuration Script
These are the basic steps need to be performed by your auth script. The code below is commented to help understand what each step is for.
- Set Wired Autoconfig (dot3svc) service startup to Auto
- Start Wired Autoconfig
- Import Configuration Profile
- Import Certificates
- Force adapter authentication event
You may be looking at this and wonder why I’m creating a Batch file instead of using PowerShell. Well, I made one with PowerShell but found that our Windows 7 machines had PowerShell 3.0 installed and some of my cmdlets wouldn’t work. The Batch file is robust enough to just work in all cases, so it wins. Plus, it’s easier for anyone to edit/support without needing PowerShell skills. Who knows, I may post the PS code at the end of the series.
Save this code as ImportComputerAuthProfile.bat
| |
Creating a Computer Authentication Profile
Each LAN interface can only have 1 Profile applied to it at any time. If you manually configure the profile then apply GPO, the GPO profile will take the place of the local profile. More on this in the Tips and Tricks post. When you are first configuring and testing your script, it may be helpful to take the working GPO profile and use it to start with, however, if you need to make any customizations or adjustments to the profile, be sure to work from a machine that doesn’t have an 802.1x GPO applied. Also, your script will fail to import your custom profile if an 802.1x GPO is applied, so you will need a non-GPO machine to test with anyway.
Group Policy Created Profile
Skip to the Export steps below
Manually Creating A Profile
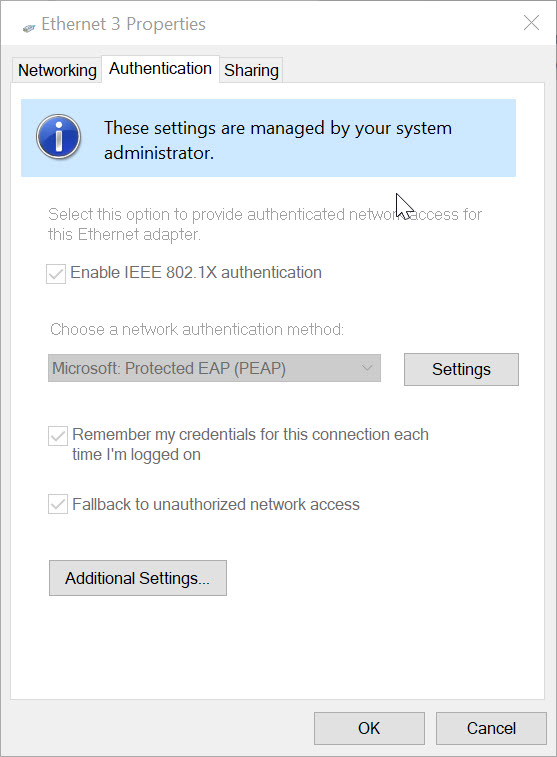
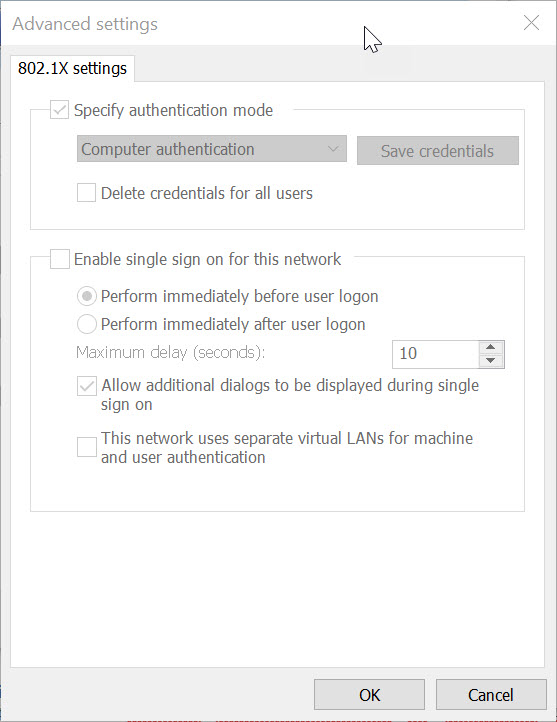
Start this process on a clean machine that doesn’t have IEEE 802.1x Policies applied, otherwise you will have trouble. You can configure 802.1x Authentication on your LAN adapter in Windows by going to the Network Connections pane in the Control Panel. From there, right click on the adapter and click on the Authentication tab. If you don’t see it, you will need to go enable and start the Wired Autoconfig service. Now you can configure authentication to match what is expected by your 802.1x service.
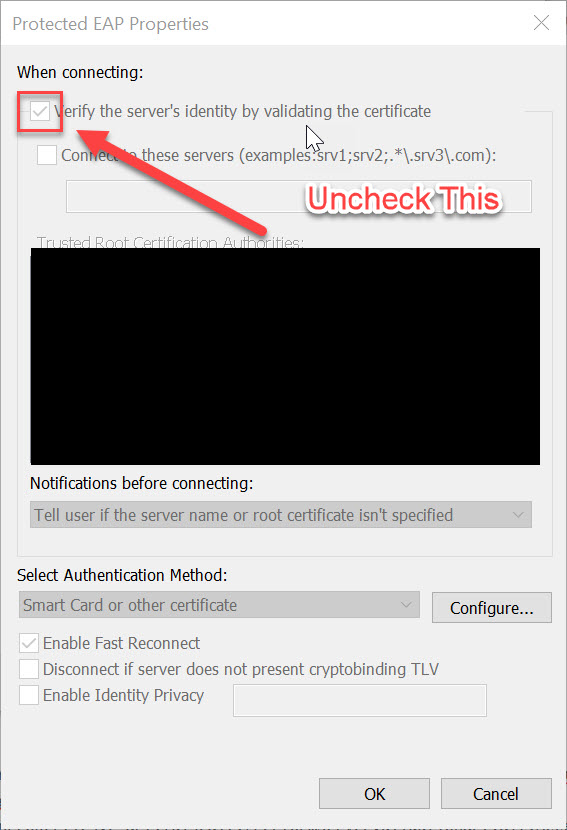
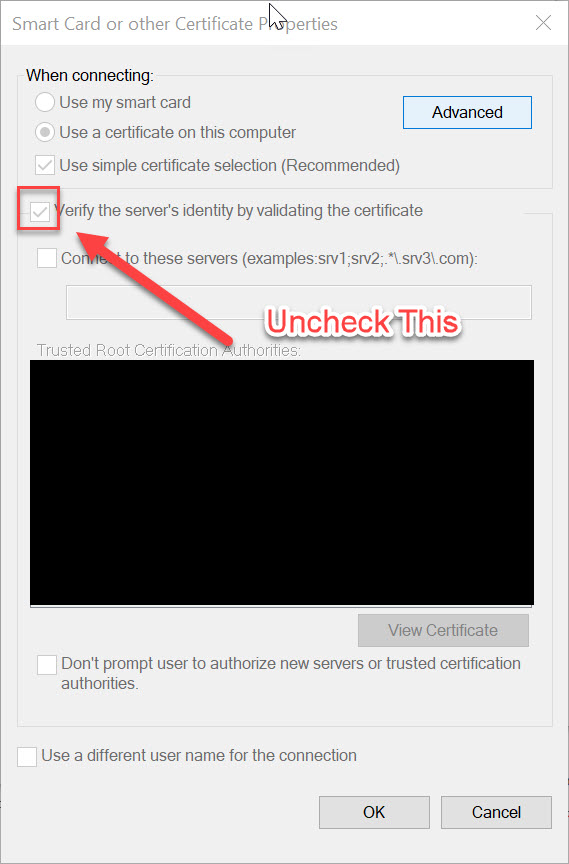
**Note:**When I exported my config then tested in Windows on another machine, it all worked fine, but when I tested in WinPE, I found that authentication would fail. I talked with my Security guy and he suggested removing the Verify server’s identity… checkboxes from the profile. Once we did that WinPE authentication began working.
To create your own profile, follow the screen shots below (Note:GPO is applied in these, so everything is greyed out).
Exporting Your Profile
Follow these steps to export your profile into an XML file.
Show the interfaces on the system.
netsh lan show interfaces
Use the interface name from the previous command in the interface=’’ parameter below
netsh lan export profile folder=c:\temp interface="Ethernet"
Grab the XML file and rename it to ComputerAuthProfile.xml and save it with your batch file.
Here’s a copy of a working WinPE Computer Authentication profile. Your mileage my vary.
| |
Gathering your Certificates
You will need to export your Root CA Certificate and a Computer certificate to use. I just went into my local certificate store and exported them. The root cert should be a .cer extension. The computer cert (Client Authentication) should contain the private key and be password protected (pick any password - you will need to add it to the batch file). Save the computer cert as a .pfx extension. Name them Root.cer and ComputerAuthCert.pfx and put them in a Certs folder with your batch file. If you need help with this step, please consult The Googler, there are plenty of great resources for this.
Putting It All Together
At this point, you should have the following:
- ImportComputerAuthProfile.bat - A 802.1x configuration script (A De-ISE-ing script for Cisco ISE).
- ComputerAuthProfile.xml - A computer authentication profile XML file
- Root.cer - A valid root CA Certificate
- ComputerAuthCert.pfx - A valid computer certificate (any valid AD joined device should work)
Place all of the files into the same folder with the certificates in a sub folder named Certs. Update the batch file with the password that you selected for your computer certificate and ensure that all of the other pathing in the script matches what you have. To test, you will need a machine that doesn’t have an 802.1x group policy already applied. Run the script. You should see the adapter attempting authentication and then connect to your 802.1x network. If it fails, reconfigure and re-export the profile and or certs and try again.
Part 2 covers configuring WinPE for 802.1x.