For the past few months, there has been a community-wide push to determine the optimal approach for Offline Servicing Windows 10 media and to get Microsoft to take on more of this burden so we can get on with other tasks instead of dealing with servicing every month. Ultimately, Microsoft needs a better process for updating media each month, but until they do, all we can do is what we do best, Socially Engineer solutions. This post will cover some of the background around the Windows 10 Offline Servicing effort and specifically provide a solution to applying Dynamic Updates to your Offline serviced Windows 10 In-Place Upgrade media so that your clients don’t have to go out to the internet for the lates compatibility updates.
OSD Community Contributions
Below is a list of several folks (I’m sure there are more) that have made great progress on Offline Servicing for the community. While I would love for this to be a comprehensive guide to servicing, I believe that these folks have done a pretty great job in providing you with lots of information and strategies for servicing your image. Everything from super simple scripts to a full blown image servicing and customization tool (OSBuilder) have been written and you should find something in here that suits your needs. For me, I can’t ever leave anything alone so I have my own script to add to this list (links will be at the bottom) as well. Thank you to all of you for your support and contributions to the OSD community!
- Mike Terrill - https://miketerrill.net/2018/06/23/optimizing-win10-os-upgrade-wim-sizes/
- Johan Arwidmark - https://deploymentresearch.com/Research/Post/672/Windows-10-Servicing-Script-Creating-the-better-In-Place-upgrade-image
- Mike Marable - https://thesystemsmonkey.wordpress.com/2018/06/29/automating-windows-10-servicing/
- Marc Graham - http://blog.ctglobalservices.com/configuration-manager-sccm/mag/devicemap-and-device-inventory-failures-in-win7-to-win10-1709-in-place-upgrades/
- David Segura - https://www.osdeploy.com/osbuilder/overview
- Gary Blok - https://garytown.com/ipu-offline-dynamic-updates
The Problem with Dynamic Updates and Offline Servicing
You may have seen posts from several folks related to Devinv.dll causing issues with Upgrades and needing to be updated. Mike Terrill, Marc Graham and I all ran into issues around the same time and began talking to the community about how to get things in sync. Ultimately, we came up with several solutions, with David Segura’s being the most automated within OSBuilder. In an unrelated effort I started looking into Dynamic Updates and why they weren’t working with SCCM/ConfigMgr and wrote about a workaround as well was more detail about Dynamic Updates here: (Part 1 and Part 2). What I didn’t know at the time was that Dynamic Updates and Devinv.dll were related until Gary Blok dropped the bombshell on us - Dynamic Updates contain all of the updated setup files needed for successful In-Place Upgrades!!
Gary’s solution was simple, just extract the Dynamic Update files and replace the setup files in the Sources directory of your Windows 10 In-Place Upgrade media. The only question remaining was, what about the Dynamic Update servicing drivers?? Windows 10 1709 has 6 Dynamic Updates, but only one that makes sense to extract to Sources. So I started poking at the problem and, with the help of Gary Blok, Mike Terrill and David Segura, I think that I have a solution to this final issue of: How do we Apply the Dynamic Update Servicing Drivers to Windows 10 In-Place Upgrade media - Offline?
Well, that solution was simple as well. I had spent most of Thursday thinking about Gary’s solution and what we could about drivers then I went to bed. The next morning, it hit me. The Dynamic Updates are all CAB files and DISM can install CAB files. I quickly got on my servicing VM and tested using PowerShell Add-WindowsPackage and It Worked!! Then I had to go to the Children’s Museum for the day knowing I was sitting on the solution and it was killing me. I messaged Gary the solution and he and Mike began testing but quickly hit a snag with applying the CABs which ended up taking a day to sort out. Finally, we had a working solution - add the Dynamic Update CABS to the install.WIM just like any other packages into your install.wim, but be careful with how you loop through your cabs or you may blow up your image as Mike found out, over and over again (See below for more info on the workaround)!
Order of Servicing Steps
By now, you should already have a process that you use to service your WIMs. It should be something like this (This only covers install.wim, there are many more wims):
Without Dynamic Updates
- Mount Windows 10 ISO
- Copy ISO contents to local folder
- Extract WIM for version you want to service (This gets rid of the multiple indexes)
- Mount install.wim
- Apply Servicing Stack Update (SSU)
- Apply Latest Cumulative Update (LCU)
- Apply Flash Update
- Clean and Reset Base (Optional, but cuts down on your WIM size - it also adds a lot of extra WIM processing time)
- Add .NET 3.5 Feature (Once applied, you can’t clean and resetbase any more)
- –Removing this step - Not likely Needed – Apply SSU (Must reapply everything after .NET or post-upgrade, the OS will still think it needs these updates)
- Apply LCU
- Dismount WIM
Here’s what the solution will look like when you add in Dynamic Updates
With Dynamic Updates
- Mount Windows 10 ISO
- Copy ISO contents to local folder
- Extract WIM for version you want to service
- Mount install.wim
- Apply Servicing Stack Update (SSU)
- Apply Latest Cumulative Update (LCU)
- Apply Flash Update
- Apply Dynamic Update Component Update (DUCU) (May or may not need to apply here)
- Clean and Reset Base
- Add .NET 3.5 Feature
- –Removing this step - Not likely Needed – Apply SSU (Must reapply everything after .NET or post-upgrade, the OS will still think it needs these updates)
- Apply LCU
- Apply Dynamic Updates Component Update (DUCU)
- Dismount WIM
- Extract Dynamic Update Setup Update (DUSU) and copy to Sources folder in your In-Place Upgrade media (Gary’s steps from post above)
Dynamic Update Types
I the absence of official Microsoft documentation, I’m going to make some stuff up.
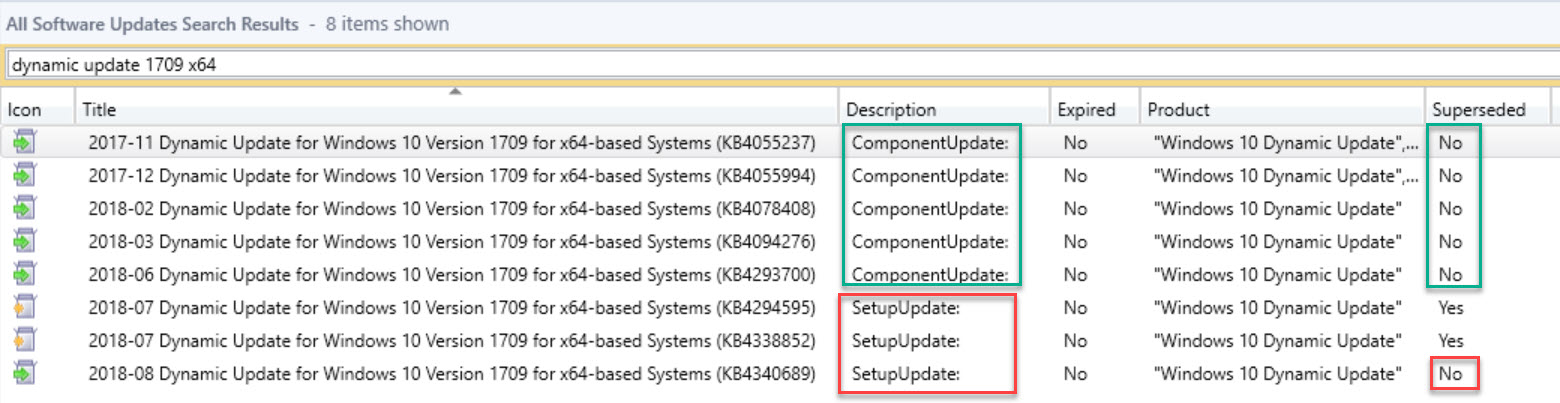
If you search in your ConfigMgr console and turn on a few extra columns, you will see that the Dynamic Updates have 2 categories Setup Updates and Component Updates. Also, only the Setup Updates ever seem to get superseded, while the Component Updates are all still current.
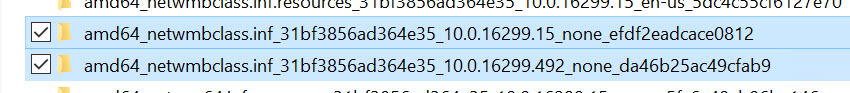
When you extract them, you find that the Setup Updates are replacement files for items in the Sources directory of your Windows 10 In-Place Upgrade media. If you extract the Component Updates, you will see that they contain various drivers and such. These items all have older, corresponding items in your install.wim. As you can see in this screenshot, I mounted my install.wim then applied one of the Dynamic Update Component Update CABs and you can see the old and new files side by side.
So, you need to get the latest Setup Update and any other Component Updates and apply them to your WIM.
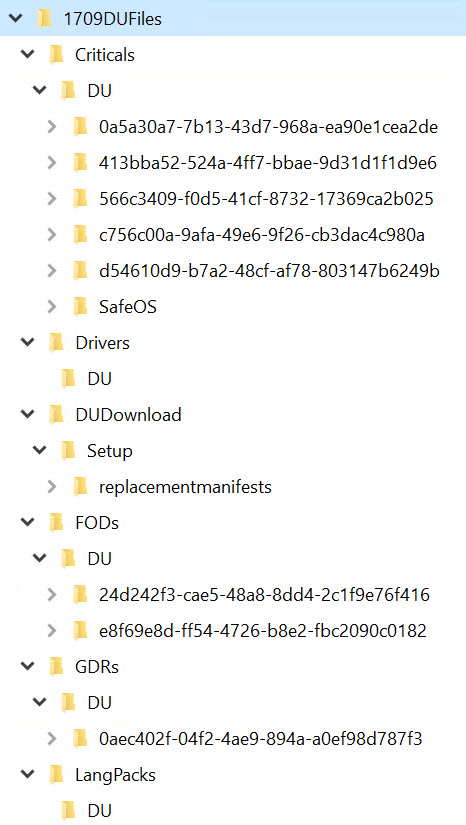
Side Note: If you launch Windows Setup.exe and begin the wizard, you have the option the download the latest updates - this gets the latest Dynamic Updates AND the latest Cumulative Update for the OS you are installing. So if you are installing an un-serviced image and enable Dynamic Updates, your client will go out to the internet and download an ~800 MB payload. If you check your C:$Windows.~BT folder before you complete the wizard and begin your install, you will find the following new folders. If you expand them, you will find that their contents match the contents of the Dynamic Updates that you are going to use for servicing here (What an amazing coincidence!)!!
]Also, you can watch your c:\Windows\WindowsUpdate.log (On Windows 7) live in CMTrace and watch Windows Update go out and get the Dynamic Updates. On Windows 10 you have to run Get-WindowsUpdateLog or something silly to get a log. (Sorry, don’t have a screenshot yet)
Getting Dynamic Updates
I’ve reached out to Microsoft to see if they can help with a publicly available URL for Dynamic Update downloads, and if you have any info, please let me know - the only way to get the download links for Dynamic Updates is by enabling them in SCCM or in WSUS. See Gary’s post above for more details on how to enable and download the updates. If you have Dynamic Updates enabled and can see them in your SCCM console, then you can either manually download them or use this handy script that I wrote cause I’m too lazy! Get the scripts and save them somewhere. You will want to separate them by OS Version and Architecture.
Grab the latest copy from GitHub
https://github.com/AdamGrossTX/PowershellScripts/blob/master/Windows%2010%20Servicing/Get-DynamicUpdates.ps1
Applying Dynamic Updates
Following the steps above, you can simply download the Dynamic Updates then apply them at the proper step when servicing your WIM. I honestly don’t know whether it matters if you apply them before cleaning and resetting the WIM (Mike Terrill doesn’t even clean and reset - we are all doing what seems best for our scenario). Either way, just use the same commands you are using to add your other updates. Here are some samples:
Each of these process a single update at a time, so you’d need to add one line per KB.
PowerShell
| |
Command Prompt (DISM.exe)
| |
You can also use this command in PowerShell to get the contents of your update folder then loop through each one for a more dynamic approach.
| |
ERRORS
The commands below caused Mike Terrill and I a lot of headache. They are equivalent commands in PowerShell and with DISM.exe to recurse through a folder and apply each update found in the folder. These are the same as the much longer ForEach PowerShell approach above. However, no matter how we tried to apply the updates, if we used the commands below, when we got to the last KB for 1709 x64, DISM would report that the WIM was corrupt and that we should start over.
PowerShell
| |
Command Prompt (DISM.exe)
| |
Here’s the full error we got:
| |
Also, be sure to get the Setup Update and extract the cab contents to your Sources folder using:
| |
Putting It All Together
As I said at the beginning, this has been a huge effort by the community to pull together the optimal process for updating our Windows media. Everything in this script was Stolen With Pride (© Johan Arwidmark) from the community. Please read through it and ask questions and send me feedback (or even push PR’s on GitHub).
NOTE: I used to have a copy of the script inline here but since I’ve updated it a few times, I’ve decided to just host it on GitHub. You can find the latest version the script and related files there. Get the latest copy from GitHub here.
So, that’s it for now. We all still have more testing to do but I believe we are in the home stretch. Please try this out and let us know how we can improve things. I know that David Segura is planning to update OSBuilder to add these features in, so be on the lookout for that. Mike Terrill was also going to do more testing and let me know how imaging goes. I’m sure I’ve missed some things or left some bugs in my code, so please be kind and let me know if you find anything. Happy Imaging!