There are numerous types of application and deployment options in ConfigMgr/SCCM today. Everything from traditional MSI to the new MSIX and Windows Store apps. Throw in Co-Management and Intune and you get even more options. Deployments can be targeted to specific devices and users. Most companies use some mix of these to get software onto devices. Some people even still refuse to use the Application model in ConfigMgr in favor of the Package model because of that one time they had trouble with it back in 2012.
For today’s adventure, I decided that I wanted to understand how to make User applications show up in Software Center (All testing was done on 1806 and 1810 TP without the Application Catalog role installed). I had been trying to instruct our Licensing team on how to help users who call about missing applications in Software Center. I started digging and ended up here.
AD Group Based User Collection
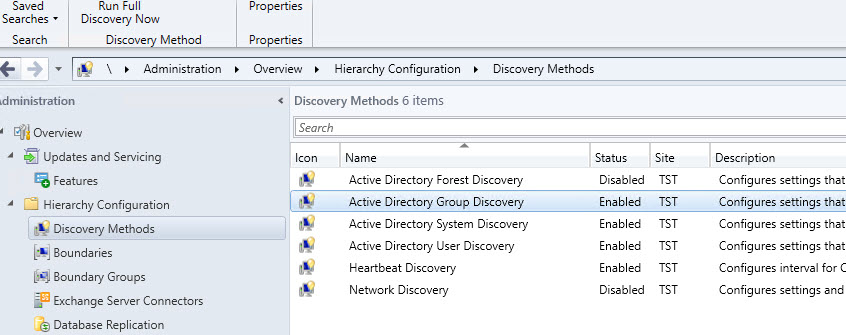
Recently on Twitter, we had some great discussion about using Active Directory Security Groups as direct (instead of query membership) members in ConfigMgr user collections and several people were surprised that this was an option or were just doing it an a sub-optimal way using query memberships. There’s great write-up by Nicke Källén about it here that got me on the right track months ago. If you haven’t read it, you should do that before proceeding because this information will build on that post.
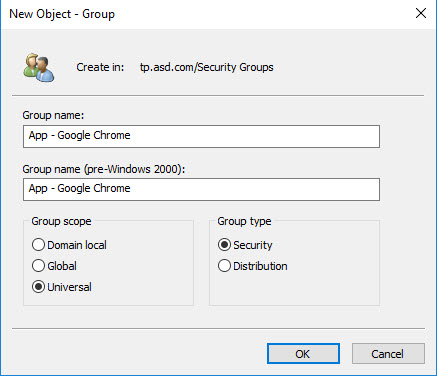
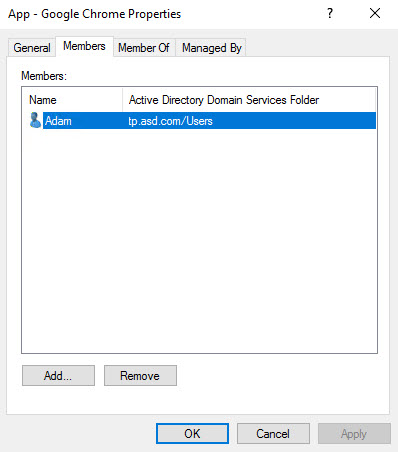
In Active Directory, create new security group called App - Google Chrome.
All of my user application collections will start with the App - prefix to enable me to quickly identify them in AD and in the ConfigMgr console.
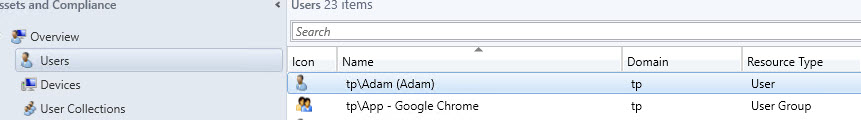
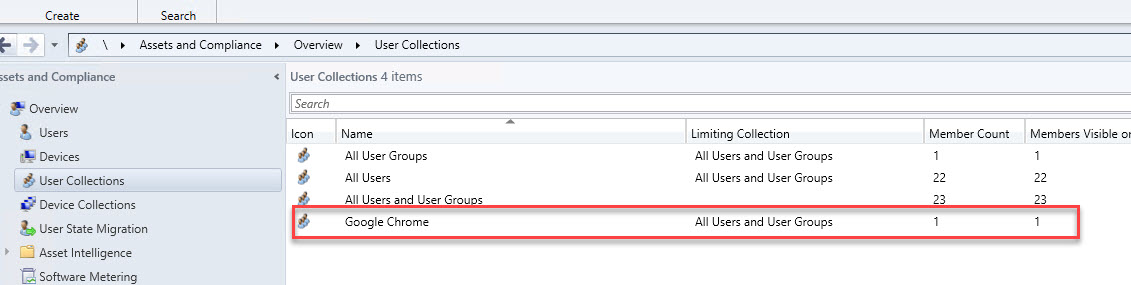
 node in the console and you should see your new AD Group.
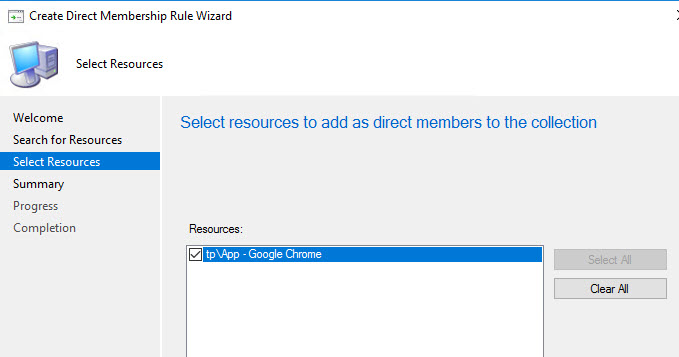
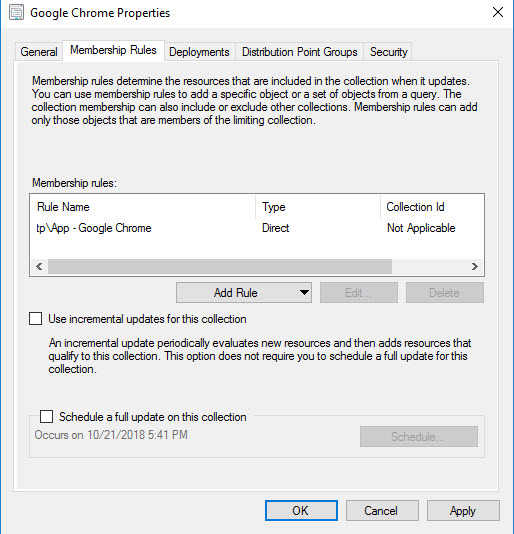
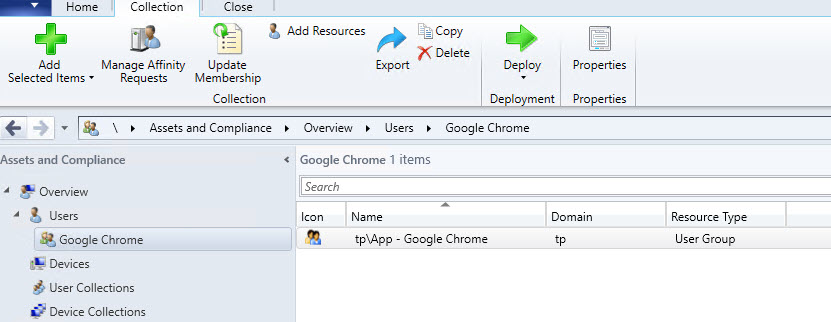
In the ConfigMgr console, create a new User Collection called Google Chrome. Set the limiting collection to All User Groups (unless you plan to add user direct User memberships as well as Groups). Then add a Direct rule. Select AD Group Resource then type % into the search box and click Search. You should see your new group.
Select the group and complete the wizard and close the collection. Once the collection membership updates, the AD group should be the only member.
Deploying Applications to User Collections
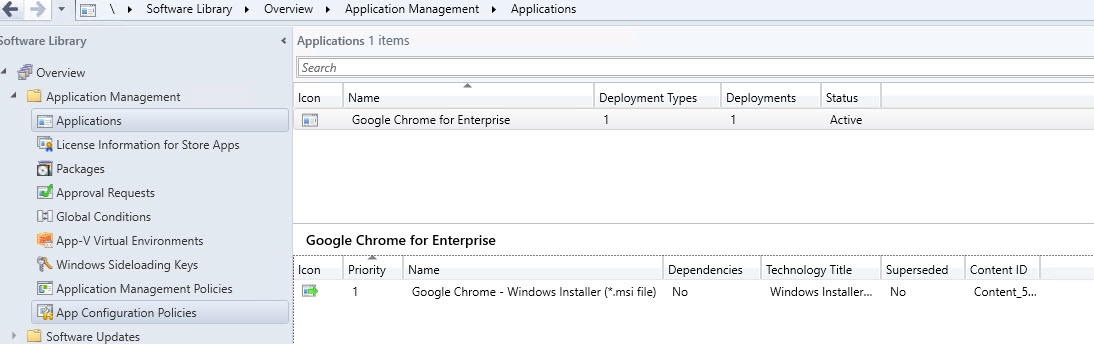
For this example, I have create a standard MSI application for Google Chrome for Enterprise, but any application will work. Simply create a new Available deployment to your new user collection. I will touch on Required in a moment.
Instant Application Delivery
At this stage, you have an AD group with no users, a User Collection and a deployment to that collection. You should be logged in with your test account and have Software Center closed. Add your test account to your AD Security group.
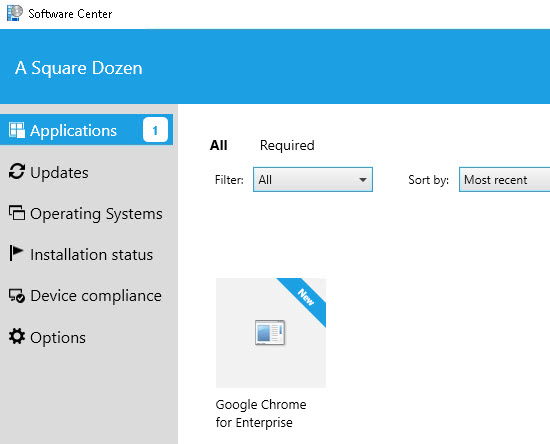
Wait however long you think your AD replication takes. In my lab, there’s no delay, so this is immediate. Lock then Unlock Windows. Open Software Center. Your app should be there.
User Available Application Using AD Security Group Membership
Let’s Look at the Logs
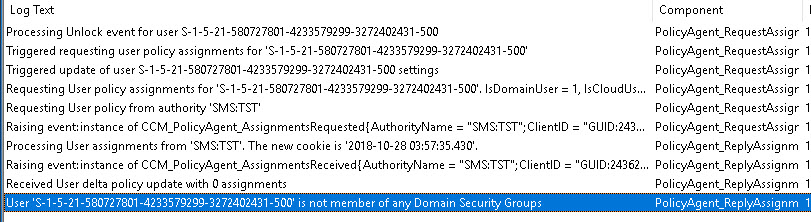
To see what’s going on, first, remove your user account from the AD group then Lock and Unlock again. Open PolicyAgent.log in CMTrace and check the box to Ignore existing lines so you can get a fresh look. Open Software Center. The application should be gone. Now check the log. (Note, my account is not a member of any AD groups at this moment.) Here’s what you should see.
These are the key entries we are looking for:
| |
As you can see, the Unlock event triggers a User Policy update. To me, this is the hidden gem in the whole process. Understanding that a machine unlock event will trigger a user policy update, helps communicate a simple process to users who request software.
Now, add the Test user account back to the AD Group and repeat the process. PolicyAgent.log will show that your account was a member of X security groups in the previous entry and the new entry will show X+1. During this refresh, PolicyAgent checked for new group memberships and then performed a delta policy update. However, unlike Machine policies where you can look in WMI and see all of the advertisements listed, this policy update is only concerned about your AD Group membership.
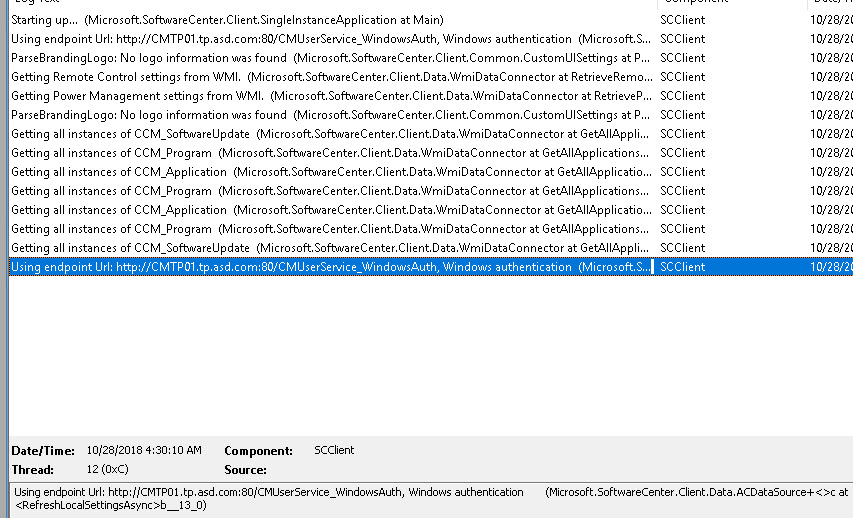
Next, switch over to the most current SCClient log. Mine is called SCClient_tp@Adam_2.log. When you open Software Center, you can see SCClient checking WMI for applications then it also uses the CMUserService_WindowsAuth web service to check for user advertisements.
At this point, I spent hours digging through WMI and even mounting the SQL Compact Edition databases that the ConfigMgr client uses and I never found any indication of User Available applications on the device until they get installed. To test my web query theory (stop rhyming now, I mean it!), I disconnected my NIC then opened Software Center. All User Available applications disappeared!! This behavior further confirms that they User Available applications in Software Center are truly dynamic.
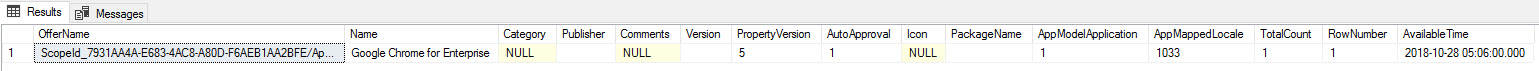
Then I watched the DB using SQL Query Analyzer and found that the client uses a query to check for User Advertisements. You can see that it calls the Stored Procedure usp_GetApplicationsTargetedToUserFiltered and passes in the user SID as well as the AD Security Group SIDs that it discovered when you unlocked the device.
Then I watched the DB using SQL Query Analyzer and found that the client uses a query to check for User Advertisements. You can see that it calls the Stored Procedure usp_GetApplicationsTargetedToUserFiltered and passes in the user SID as well as the AD Security Group SIDs that it discovered when you unlocked the device.
| |
I manually ran this query in SQL and got this result:
You could dig into the SQL Stored Procedure and build a report using the same functions and queries, I just haven’t gotten THAT far into it.
User Required Applications
The behavior I noticed for Required applications was slightly different. While Available applications required you to open Software Center, Required applications began installing almost immediately after unlocking. (Note, I left Software Center open for the video, but even with it closed, the application will auto install just after unlock.)
What Does This All Mean?
If you’ve used ConfigMgr for any length of time, you know that most Software Center related delays are a result of Collection Membership Updates and Client Policy Processing. In my environment, our collections take ~30 mins to process fully. We have a web portal for users to request applications that adds their devices to collections, updates membership then triggers client policy updates. This has always lead to users complaining that their apps aren’t available yet. If we were to switch over to User Available application deployments, we could reduce the number of wasted hours trying to make applications show up for impatient users. I know there are licensing and other issues that potentially cause this to fall apart for some companies/applications, but User-based Application deployments should be the norm. Windows Store for Business, Intune and AutoPilot are all User-Centric in their application delivery and moving ConfigMgr over to the same model should help us stay current with Modern Device Management. It sure will make hardware lifecycle and device replacements much less painful for users.